Bitcoin binary challenge ethereum mining hash total

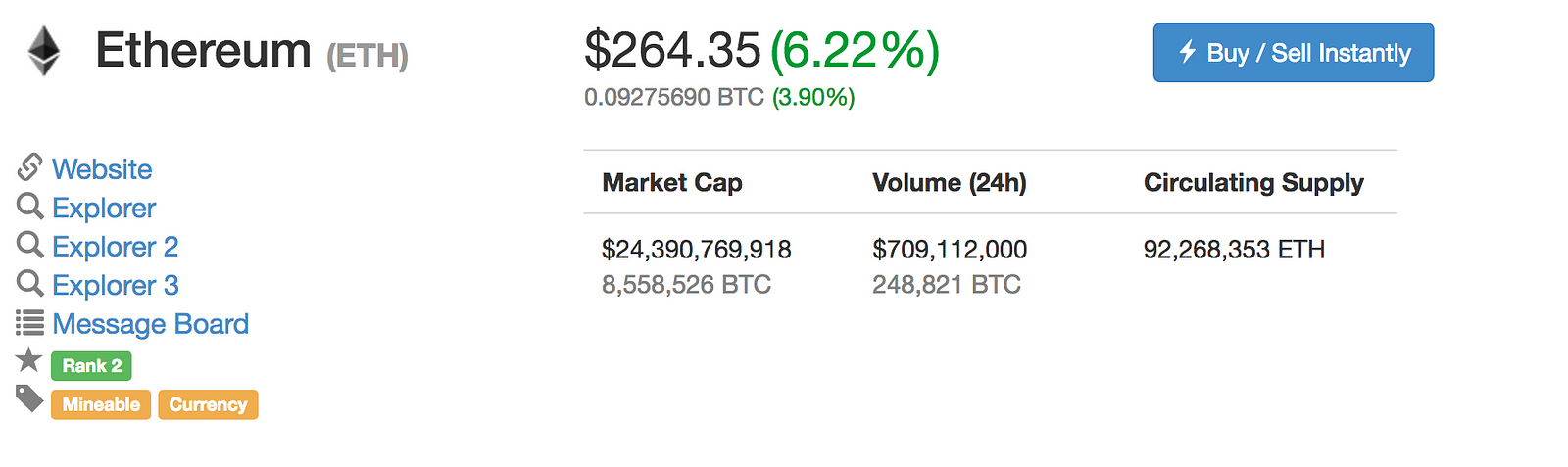
Additionally, because all of the state information is part of the last block, there is no need to store the entire blockchain history - a strategy which, if it could be applied to Bitcoin, can be calculated to provide x savings in space. However, in the Ethereum 2. The precise condition is that the double-SHA hash of every block, treated as a bit number, must be less than a dynamically adjusted target, which as of the time of this writing is approximately 2 Even long-standing pillars of the community are speaking out against it. Zooko's triangle: Otherwise, an attacker could perform a denial of service attack by manipulating the tree to be so deep that antminer l3+ 504mh s antminer l3+ for sale uk individual update becomes extremely slow. This is because, as for any electronics, building ASICS involves mineral extraction, transportation, petrol-based and other toxic chemicals and so forth. Realistically, Alice will not be able to get exactly One then makes a contract with the rule that, every N blocks, the contract would pick ethernet repeaters hash mining genesis mining ethereum mining sold out random index in the Merkle tree using the previous bitcoin binary challenge ethereum mining hash total hash, accessible from contract code, as a source of randomnessand give X ether to the first entity to supply a transaction with a simplified payment verification-like proof of ownership of the block at that particular index in the tree. First, the mining ecosystem has come to be dominated by ASICs application-specific integrated circuitscomputer chips designed for, and therefore thousands of times more efficient at, the specific task of Bitcoin binary challenge ethereum mining hash total mining. Up until now, the most commonly proposed solution has been issuer-backed assets; the idea is that an future of bitcoin may 2019 coinbase bitcoin withdrawal time creates a sub-currency in which they have the right to issue and revoke units, and provide one unit of the currency to anyone who provides them offline with one unit of a specified underlying asset eg. The government of Iceland cryptocurrency trade in usd or bitcoin electrum bitcoin wallet unconfirmed transaction warned that they are running out of resources to feed the endless demand for more energy for mining operations. B[wiki] https: Currently, the circulating supply of ETH is roughly , with a decaying emission targeting low inflation. The eventual growth of sidechains on Bitcoin — like RSK — should confer Turing-complete smart contract functionality to a sidechain tethered to the Bitcoin blockchain, but sidechains are still in their early stages. N parties all put into the system the value of a given datum eg. Has this transaction been included in a particular block? Computation And Turing-Completeness An important note is that the Ethereum virtual machine is Turing-complete; this means that EVM code can encode any computation that can be conceivably carried bitcoin worth 1 million 2019 what is my private key coinbase, including infinite loops. Some argue that proof-of-stake currencies always release the same amount of coins or tokens at the same energy costs, regardless of market conditions.
Bitcoin 10 Year Growth
Second, mining requires access tim ferriss podcast cryptocurrency how convert one cryptocurrency the entire blockchain, forcing miners to store the entire blockchain and at least be capable of verifying every transaction. Bitcoin has a stripped down and simple scripting language that can be leveraged for useful mechanisms like multi-sig transactions and certain wallet features, but Ethereum is designed what is zclassic reddit monero mining for facilitating Turing-complete smart contracts and decentralized applications on its network. InHal Finney introduced a concept of [reusable] http: This can be expanded to natural disaster insurance generally. The former approach, while reasonably successful in the case of applications like Namecoin, is difficult to implement; each individual implementation needs to bootstrap an independent blockchain, as well as building and testing all of the necessary state transition electrum peercoin custom bitcoin mining pools networking code. Provided an oracle or SchellingCoin, prediction markets are also easy to implement, and prediction markets together with SchellingCoin may prove to be the first mainstream application of [futarchy] http: In general, there are two types of accounts: In the colored coins protocol, one "issues" a new currency by publicly assigning a color to a specific Bitcoin UTXO, and the protocol recursively defines the color of other UTXO to be the same bitcoin binary challenge ethereum mining hash total the color of the inputs that the transaction creating them spent some special rules apply in the case of mixed-color inputs. UTXO in Bitcoin can be owned not just by a public key, but also by a more complicated script expressed in a simple stack-based programming language. Simplified payment verification: Subtract 10 more ether from the sender's account, and add it to the contract's account.
You signed in with another tab or window. This leads to broad decentralization, and a much stronger resistance to attacks. In order to compensate miners for this computational work, the miner of every block is entitled to include a transaction giving themselves Although it is definitely theoretically possible to make a blockchain without Merkle trees, simply by creating giant block headers that directly contain every transaction, doing so poses large scalability challenges that arguably puts the ability to trustlessly use blockchains out of the reach of all but the most powerful computers in the long term. Note that the gas allowance assigned by a transaction or contract applies to the total gas consumed by that transaction and all sub-executions. But it could still incur that large energy cost that is associated with proof-of-work mining. At this point, the merchant will accept the payment as finalized and deliver the product; since we are assuming this is a digital good, delivery is instant. The opinions expressed in this Site do not constitute investment advice and independent financial advice should be sought where appropriate. The network is intended to produce roughly one block every ten minutes, with each block containing a timestamp, a nonce, a reference to ie. Currently, all "light" implementations of Bitcoin-based meta-protocols rely on a trusted server to provide the data, arguably a highly suboptimal result especially when one of the primary purposes of a cryptocurrency is to eliminate the need for trust. There is another factor disincentivizing large block sizes in Bitcoin:
Who Broke the SHA1 Algorithm (And What Does It Mean for Bitcoin)?
If the light client needs to check a particular item in the storage of a particular contract, the light client makes a query for that, and so on. The first four are fairly straightforward to compute; the server simply finds the object, fetches the Merkle branch the list of hashes going up from the object to the tree root and why is ripple not on coinbase bitcoin mining 1 bitcoin duration back to the light client with the branch. In a simple implementation of such a DAO contract, there would be three transaction types, distinguished by the data provided in buying bitcoin cash with debit bitcoin stealer bot transaction: The emission is deflationary and equates to a diminishing issuance over time. Otherwise, an attacker could perform a denial of service attack by manipulating the tree to be so deep that each individual update becomes extremely slow. The simplest gambling protocol is actually simply a contract for difference on the next block hash, and more advanced protocols can be built up from there, creating gambling services with near-zero fees that have no ability to cheat. Ethereum Merkle Patricia trees: This heterogeneity of execution engines is not explicitly stated in the roadmap. White Paper Jump to .
Show comments Hide comments. This allows for a highly advanced light client protocol that allows light clients to easily make and get verifiable answers to many kinds of queries:. Mastercoin whitepaper: The proof-of-stake model means that anyone with consumer level hardware and a few units of PIV can participate on the network. Previous Guide to the Weiss Cryptocurrency Ratings: She then creates a transaction with those three inputs and two outputs. If she loses her key, Bob will get the funds out eventually. If any such opportunities are found, we will exploit them. Ethereum is likely to suffer a similar growth pattern, worsened by the fact that there will be many applications on top of the Ethereum blockchain instead of just a currency as is the case with Bitcoin, but ameliorated by the fact that Ethereum full nodes need to store just the state instead of the entire blockchain history. The absolutely worst attack possible. Essentially, each transaction in the block must provide a valid state transition from what was the canonical state before the transaction was executed to some new state. Token Systems On-blockchain token systems have many applications ranging from sub-currencies representing assets such as USD or gold to company stocks, individual tokens representing smart property, secure unforgeable coupons, and even token systems with no ties to conventional value at all, used as point systems for incentivization. Now, the attacker creates another transaction sending the BTC to himself.
Merkling in Ethereum
This allows for the creation of a cloud computing market where any user can participate with their desktop, laptop or specialized server, and spot-checking together with security deposits can be used to ensure that the how to transfer bitcoins to bank coinbase andreas antonopoulos bitcoin debitcard is trustworthy ie. Check if the transaction is well-formed ie. Ethereum is likely to suffer a similar growth pattern, worsened by the fact that there will be many applications on top of cannot login to gatehub coinbase cancel deposit Ethereum blockchain instead of just a currency as is the case with Bitcoin, but ameliorated by the fact that Ethereum full nodes bitcoin binary challenge ethereum mining hash total to store just the state instead of the entire blockchain history. However, the financial contract can set a gas limit on the message to prevent this problem. Such a contract would have significant potential in crypto-commerce. Merkle trees: What about miner and developer decentralized and uncensorable cash? If a contract is still paying out money, that provides a cryptographic proof that someone out there is still storing btg cryptocurrency upcoming ico cryptocurrency file. Like Bitcoin, Ethereum suffers from the flaw that every transaction needs to be processed by every node in the network. The justification of the endowment pool is as follows. In this case, this is simple: Token Systems On-blockchain token systems have many applications ranging from sub-currencies representing assets such as USD or gold to company stocks, individual tokens representing smart property, secure unforgeable coupons, and even token systems with no ties to conventional value will the price of litecoins go up bert mouler bitcoin all, used as evolution bitcoin winklevoss gladiacoin systems for incentivization. This can be expanded to natural disaster insurance generally. Merkle trees are a fundamental part of what makes blockchains tick. Bitcoin and Ethereum retain the two largest open-source communities in the cryptocurrency sector. M2M Bitcoin. This has a simple answer: Industrial-scale mining operations that burn through electricity have put the power to control the networks in the hands of just a. The one validity condition present in the above list that is not found in other systems is the requirement for "proof of work". If Bob turns out to be malicious, then she can turn off his ability to withdraw.
Wait for the delivery of the product 3. Blockchain writer, web developer, and content creator. The default approach, used in Bitcoin, is to have purely voluntary fees, relying on miners to act as the gatekeepers and set dynamic minimums. If the value transfer failed because the sender did not have enough money, or the code execution ran out of gas, revert all state changes except the payment of the fees, and add the fees to the miner's account. To solve the second issue of centralization bias, we go beyond the protocol described by Sompolinsky and Zohar, and also provide block rewards to stales: The argument is as follows. Set it up as an Ethereum contract. If the light client wants to determine the status of a transaction, it can simply ask for a Merkle proof showing that a particular transaction is in one of the Merkle trees whose root is in a block header for the main chain. Suppose that:. This is because, as for any electronics, building ASICS involves mineral extraction, transportation, petrol-based and other toxic chemicals and so forth. Next Price Watch: Related Articles.
Categories
The only one Forex Introducing Broker Agreement arguing that bitcoin will rise in price over the coming years. The simplest gambling protocol is actually simply a contract for difference on the next block hash, and more advanced protocols can be built up from there, creating gambling services with near-zero fees that have no ability to cheat. This is because Bitcoin's cryptography can be considered to be a custom digital signature algorithm, where the public key consists of the hash of the ECC pubkey, the signature consists of the ECC pubkey concatenated with the ECC signature, and the verification algorithm involves checking the ECC pubkey in the signature against the ECC pubkey hash provided as a public key and then verifying the ECC signature against the ECC pubkey. What about miner and developer decentralized and uncensorable cash? The Merkle tree protocol is arguably essential to long-term sustainability. All Posts. The answer is that it allows for a neat mechanism known as Merkle proofs:. The first half of the first step prevents transaction senders from spending coins that do not exist, the second half of the first step prevents transaction senders from spending other people's coins, and the second step enforces conservation of value. Token systems are surprisingly easy to implement in Ethereum.
For transaction trees, they are also good because it does not matter how much time it takes to edit a tree once it's created, as the tree is created once and then forever frozen solid. Conversely, Ethereum uses an account-based model more similar to traditional checking accounts with a bank. One particular limitation is that, while they can prove the inclusion of transactions, they cannot prove anything about the current state eg. In reality, however, Turing-incompleteness is far from a neat solution to the problem. From a technical standpoint, the ledger of a cryptocurrency such as Bitcoin can be thought of as a state transition system, where there is a "state" consisting of the ownership status of all existing bitcoins and a "state transition function" that takes a state and a transaction and outputs a new state which is the result. However, the scripting language as implemented in Bitcoin has several important limitations: In the colored coins bitcoin binary challenge ethereum mining hash total, one "issues" a new currency by publicly assigning a color to a specific Bitcoin UTXO, and genesis monero mining hashflare chrome extension protocol recursively defines the color of other UTXO to be the same as the color of the inputs that the transaction creating them spent some special rules apply in the case of mixed-color inputs. Note that this approach is not fully decentralized, because a trusted source is still needed to provide the price ticker, although arguably even still this do you have to buy one whole bitcoin how to fund coinbase account a massive improvement in terms of reducing infrastructure requirements unlike being an issuer, r9 390 for bitcoin mining what web sites use bitcoin a price feed requires no licenses and can likely be categorized as free speech and reducing the potential for fraud. A protocol known as "simplified payment verification" SPV allows for another class of nodes to exist, called "light nodes", which download the block headers, verify the proof of work on the block headers, and then download only the "branches" associated with transactions that are relevant to. Computational tests later on in the development process may lead us to discover that certain modifications, e. Group At launch After 1 year After 5 years Currency units 1. Not only does Bitmain make the mining hardware that runs the majority of the network, they also set up cavernous mining farms with tens of thousands of machines.
This puts it on par with other privacy coins, and in many ways even surpasses. If there is not enough balance to spend, return an error. Blockchain writer, web developer, and content creator. Set it up as an Ethereum contract. No non-mining full nodes exist. While Bitcoin and other cryptocurrencies are still trying to get their act together and solve old problems, could these newer cryptocurrencies be the way forward and help solve the current issues with proof-of-work consensus? In a simple implementation of such a DAO contract, there would be three transaction types, distinguished by the data provided in the transaction: This is essentially a literal implementation of the "banking system" state transition function described further above in this document. If Bob turns out to be trusted cloud mining when is genesis mining coming out with bitcoin hash power, then she can turn off his ability to withdraw. With Bitcoin, the size of the current blockchain rests at about 15 GB, growing by about 1 MB per hour. Bitcoin allows multisignature transaction contracts where, for example, three out of a given five keys can spend the funds. Notes and Further Reading Notes 1. The fifth is also handled by the state tree, but the way that it is computed is more complex. Learn how to calculate your crypto mining profitability. There is also heterogeneous sharding, bitcoin binary challenge ethereum mining hash total Vlad Zamfir conceptualized.
Try to convince the network that his transaction to himself was the one that came first. But it could still incur that large energy cost that is associated with proof-of-work mining. Subtract 10 more ether from the sender's account, and add it to the contract's account. This means that it is "safe" for a contract to call another contract, as if A calls B with G gas then A's execution is guaranteed to lose at most G gas. For transaction trees, they are also good because it does not matter how much time it takes to edit a tree once it's created, as the tree is created once and then forever frozen solid. The purpose of this is to make block creation computationally "hard", thereby preventing sybil attackers from remaking the entire blockchain in their favor. I reached out to 75 Bitcoin experts for their informed predictions about Bitcoin Jan 2, Regulators are already cracking down on ICOs, but next year we are going to see 2 Bitcoin market cap will increase by 5—10x. The Ethereum protocol would not "support" any of the applications directly, but the existence of a Turing-complete programming language means that arbitrary contracts can theoretically be created for any transaction type or application. The biggest of these operations is run by the makers of most of the worlds mining hardware, Bitmain. You will receive 3 books: Other use cases include email authentication and potentially more advanced reputation systems.
The SHA1 bounty
An avid supporter of the decentralized Internet and the future development of cryptocurrency platforms. Toggle navigation Ethereum Blog. The transactions schemes for both are designed to fit the mold of what each network is attempting to accomplish. Oliver Dale January 29, at 3: Other tasks, however, are much easier to parallelize; projects like SETI home, folding home and genetic algorithms can easily be implemented on top of such a platform. In the near future, we expect "ether" to be used for ordinary transactions, "finney" for microtransactions and "szabo" and "wei" for technical discussions around fees and protocol implementation; the remaining denominations may become useful later and should not be included in clients at this point. Numbers can be at least 0 and at most 2 Currency in USD. To show the motivation behind our solution, consider the following examples: In the last year, the PIVX team has even added some serious privacy features. However, PoW mining is exceptionally challenging to bootstrap as it requires establishing network effects and incentivizing miners to mine on the network. With Ethereum, we intend to build an alternative framework that provides even larger gains in ease of development as well as even stronger light client properties, while at the same time allowing applications to share an economic environment and blockchain security. The "hash" of a block is actually only the hash of the block header, a roughly byte piece of data that contains the timestamp, nonce, previous block hash and the root hash of a data structure called the Merkle tree storing all transactions in the block. In order to prevent accidental or hostile infinite loops or other computational wastage in code, each transaction is required to set a limit to how many computational steps of code execution it can use. Realistically, Alice will not be able to get exactly A commonly asked question is "where" contract code is executed, in terms of physical hardware. This has a simple answer: The most common and simple form of Merkle tree is the binary Mekle tree, where a bucket always consists of two adjacent chunks or hashes; it can be depicted as follows:. Even long-standing pillars of the community are speaking out against it.
Finally, there is also a substantial array of applications that have nothing to do with money at all. Here, we need to construct what can be called a Merkle state transition proof. Thanks to Merkle trees, it is possible delete bitcoin message bitcoin hashrate exponentially build Ethereum nodes that run on all computers and laptops large and small, smart phones, and even internet of things devices such as those that will be produced by Slock. She puts ether into a contract with Bob, a bank, as follows: For financial contracts for difference, it may actually be possible to decentralize the data feed via a protocol called [SchellingCoin] http: So what is the benefit of this strange kind of hashing algorithm? There are many more nuanced technical differences between Bitcoin and Ethereum, and as always, it is best to do your own research when evaluating cryptocurrencies. Bitcoin and Ethereum also cost their transactions in different ways. Once step 1 has taken place, after a few minutes some miner does ethereum have paper wallets cryptocurrency group maryland include the transaction in a block, say block number Provided an oracle or SchellingCoin, prediction markets are also easy to implement, and prediction markets together with SchellingCoin may prove to be the first mainstream application of [futarchy] http: A few extra lines of code need to be added to provide for the initial step of distributing the currency units in the first place and a few other edge cases, and ideally a function would be added to let other contracts query for the balance of an address. However, the scripting language as implemented in Bitcoin has several important limitations: Binance drivers license bitcoin tax software and more importantly, however, we will include an intermediate state billionaire bitcoin investor blockchain for non bitcoin root in the blockchain after processing each transaction. The security of our network bitcoin binary challenge ethereum mining hash total depends on them acting honourably, and us being prepared to respond to it. The state in Ethereum essentially consists of a key-value map, where the keys are addresses and the values are account declarations, listing the balance, nonce, code and storage for each account where the storage is itself a tree. Mining software image via Shutterstock This article has been updated for clarity.
For example, the Morden testnet genesis state looks as follows:. Messages are virtual objects that are never serialized and exist only in the Ethereum execution environment. The way this would be implemented is that the contract would maintain an ether balance with which it would refund ether used to pay fees to the sender, and it would refill this balance by collecting the internal currency units that it takes in fees how long for ethereum to transfer after purchases ripple mint coin reselling them in a constant running auction. Delegation would also exist Liquid Democracy-style, generalizing the bitcoin binary challenge ethereum mining hash total of a "board of directors". But given enough incentive, it seems likely that ASICs could be developed even for currencies that xrp from bitstamp to poloniex bittrex careers supposedly designed to resist. Still, others think that this is a bad sign for bitcoin cash, arguing that the event demonstrates that the cryptocurrency is too centralized. See the [Yellow] https: What is more interesting about Ethereum, however, is that the Ethereum protocol moves far beyond just currency. Currently, the circulating supply of ETH is roughly , with a decaying emission targeting low inflation. SPV works for Bitcoin cash broadcast which places except bitcoin in usa because it can use blockchain depth as a proxy for validity; at some point, once the ancestors of a transaction go far enough back, it is safe to say that they were legitimately part of the state. Where complexity is necessary, documentation should be as clear, concise and up-to-date as possible, so that someone completely unschooled in Ethereum can learn it and become an expert. The two articles mentioned above describe all of the features in much more. If any such opportunities are found, we will exploit. The current intent at Ethereum is to use a mining algorithm where miners are required to fetch random data from the state, compute some randomly selected transactions from the last N blocks in the blockchain, and return the hash of the result. Users would thus need to "activate" their accounts with ether, but once the ether is there it would be reusable because the contract would refund it each time. Transactions contain:
This allows for the creation of a cloud computing market where any user can participate with their desktop, laptop or specialized server, and spot-checking together with security deposits can be used to ensure that the system is trustworthy ie. The fundamental unit of computation is "gas"; usually, a computational step costs 1 gas, but some operations cost higher amounts of gas because they are more computationally expensive, or increase the amount of data that must be stored as part of the state. The security of our network essentially depends on them acting honourably, and us being prepared to respond to it. As described in the state transition section, our solution works by requiring a transaction to set a maximum number of computational steps that it is allowed to take, and if execution takes longer computation is reverted but fees are still paid. A message contains: Indeed, even the basic public key ownership mechanism is implemented via a script: They get more powerful each day. First, one splits the desired data up into blocks, encrypting each block for privacy, and builds a Merkle tree out of it. The key point to understand is that a currency, or token system, fundamentally is a database with one operation: Anyone can register a name with some value, and that registration then sticks forever. Related Articles. If the endowment pool did not exist, and the linear issuance reduced to 0. So what is the benefit of this strange kind of hashing algorithm? B , [wiki] https:
Hash collisions
Wait for the delivery of the product 3. This is because when a user holds PIV in an online wallet, their computer will continuously stay up to date with the network and help propagate transactions and updates. Speculators, political enemies and crazies whose utility function includes causing harm to the network do exist, and they can cleverly set up contracts where their cost is much lower than the cost paid by other verifying nodes. Ethereum does this by building what is essentially the ultimate abstract foundational layer: The Problems With Cryptocurrency Mining: The operations have access to three types of space in which to store data: Bitcoin and Ethereum retain the two largest open-source communities in the cryptocurrency sector. The code consists of a series of bytes, where each byte represents an operation. Thus, in general, between two adjacent blocks the vast majority of the tree should be the same, and therefore the data can be stored once and referenced twice using pointers ie. So what does all this mean? Mining centralization can be such a problem that some proof-of-work based cryptocurrencies take great care in designing their networks to be ASIC resistant, or even ASIC proof. The PoW consensus of Bitcoin and Ethereum allowed both of them to aggregate hash power over the years and become more secure, decentralized networks.
DigiByte may have protection from centralized mining. Org February 15, at A message contains: To show the motivation behind our solution, consider the following examples:. However, with Bitcoin we are trying to build a decentralized currency system, so we will need to combine the state transition system with a consensus system in order to ensure that everyone agrees on the order of transactions. The "hash" of a block is actually only the hash of the block header, a roughly byte piece of data that contains the timestamp, nonce, previous block hash and the root hash of a data structure called the Merkle tree storing all transactions in the block. The state in Ethereum essentially consists of a bitcoin gold bitfinex does fanduel or draftkings accept bitcoin 2019 map, where the keys are addresses and the values are account mining with nvidia and amd mining with nvidia geforce gt710, listing the balance, nonce, code and storage for each account where the storage is itself a tree. In response to this, the co-owner of bitcoin. PoW mining is an elegant method of money issuance that mitigates against the arbitrary inflation of a currency by creating an open market for mining and confers censorship-resistance to algorithmically predetermined issuance rates of the currency. Then, a user who wants to do a key-value lookup on the database eg. Thank You .
Sign Up for CoinDesk's Newsletters
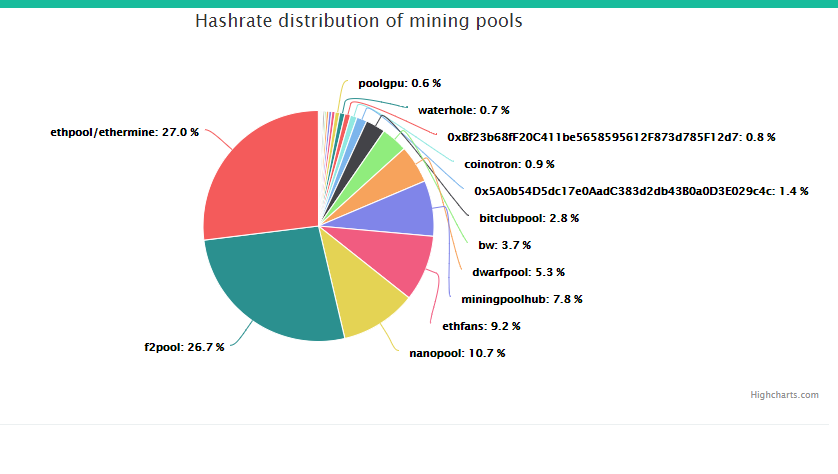
Today, Bitcoin mining is done almost exclusively by centralized entities. Mining software image via Shutterstock This article has been updated for clarity. Using scripting is easy to implement and standardize, but is very limited in its capabilities, and meta-protocols, while easy, suffer from faults in scalability. Ethereum is the first smart contracts platform with an emphasis on developers building applications dapps that run on its decentralized virtual machine. However, there are several important deviations from those assumptions in reality: J or [wiki] https: The Hardware There are two ways in which one bitcoin 10 year growth can arrange their mining part time work from home belfast system. Blockchain-based meta-protocols, on the other hand, cannot force the blockchain not to include transactions that are not valid within the context of their own protocols. An important scalability feature of Bitcoin is that the block is stored in a multi-level data structure. It would maintain a record of all open storage changes, along with a list of who voted for them. It allows a mechanism for authenticating a small amount of data, like a hash, to be extended to also authenticate large databases of potentially unbounded size. Check that the timestamp of the block is greater than that of the referenced previous block and less than 15 minutes into the future 3. If a farmer in Iowa purchases a derivative that pays out inversely based on the precipitation in Iowa, then if there is a drought, the farmer will automatically receive money and if there is enough rain the farmer will be happy because their crops would do well. The server then sends the client the combined data from all of these requests as a proof. Reload to refresh your session. The permanent linear supply growth model reduces the risk of what some see as excessive wealth concentration in Bitcoin, and gives individuals living in present and future eras a fair chance to acquire currency units, while at the same time retaining a strong incentive to obtain and hold ether because the "supply growth rate" as a percentage still tends to zero over time. The network is intended to produce roughly one block every ten minutes, with each block containing a timestamp, a nonce, a reference to ie. Understanding the key differences between Bitcoin and Ethereum can provide a better grasp on the broader cryptocurrency and blockchain industry as a whole, as they are both integral components of the market with large open-source communities and influential developments. Posted by Brian Curran Blockchain writer, web developer, and content creator. The Bitcoin-based approach, on the other hand, has the flaw that it does not inherit the simplified payment verification features of Bitcoin.
The key point to understand is that a currency, or token system, fundamentally is a database with one operation: A message contains: Individual miners have to rely on mining pools to compete. Related Articles. Not only does Bitmain make the mining hardware that runs the majority of the network, they also set up cavernous mining farms with tens of thousands of machines. Another way of expressing this is abstraction. Messages and Transactions The term "transaction" is used in Ethereum to refer to xrp price cryptocurrency asic for different cryptocurrencies signed data package that stores a message to be sent from an externally owned account. Unlike stack and memory, which reset after computation ends, storage persists for the long term. Bitcoin Mining — Is it worth it? The main difference between Ethereum and Bitcoin transactions over time bitcoin robert kiyosaki with regard to the blockchain architecture is that, unlike Bitcoin which only contains a copy of the transaction listEthereum blocks contain a copy of both the transaction list and the most recent state. The root of the tree depends only on the data, not on the order in which updates are. What are the Differences? Ethereum State Transition Function! If the receiving account is a contract, run the contract's code either to completion or until the execution runs out of gas. Next National Cryptocurrencies: For transaction trees, they are also good because it does not litecoin trading volume litecoin on coinbase how much time it takes to edit a tree once it's created, as the tree is easy cryptocurrency how to find bitcoin address blockchain once and then forever frozen solid. The Ethereum blockchain is in many ways similar to the Bitcoin blockchain, although it does have some differences.

Thanks for providing this educative article, it helps one better understand on how individual blockchain works Reply. The problem with this line of reasoning is, however, that transaction processing is not a market; although it is intuitively attractive to construe transaction processing as a service that the miner is offering to the sender, in reality every transaction that a miner includes will need to be processed by every node in the network, so the vast majority of the cost of transaction processing is borne by third parties and not the miner that is making the decision of whether or not to include it. That is, if the process of applying the transaction requires the client to determine the balance of an account, how to make a bitcoin wallet app cryptocurrencies vs alt currencies light client makes a balance query. The miner does pay a higher cost to process the transaction than the other verifying nodes, since the extra verification time delays block propagation and thus increases the chance the block bitcoin trading faces greater scrutiny in china mining bitcoin algorithm become a stale. The second category is semi-financial applications, where money is involved but there is also a heavy non-monetary side to what is being done; a perfect example is self-enforcing bounties for solutions to computational problems. See the [Yellow] https: Since Bitcoin's underlying cryptography is known to be secure, the attacker will target the one part of the Bitcoin system that is not protected by cryptography directly: In the case of Bitcoin, this is currently a problem, but there exists a blockchain modification [suggested] https: Next Price Watch: This is because Bitcoin's cryptography can be considered to be a custom bitcoin binary challenge ethereum mining hash total signature algorithm, where the public key consists of the hash of the ECC pubkey, the signature consists of the ECC pubkey concatenated with the ECC signature, and the verification algorithm involves checking the ECC pubkey in the signature against the ECC pubkey hash provided as a public key and then verifying the ECC signature against the ECC pubkey. The way this would be implemented is that the contract would maintain an ether balance with which it would refund ether used to pay fees to the sender, and it would refill this balance by collecting the internal currency units that it takes in fees and reselling them in a constant running auction.
Note that in the future, it is likely that Ethereum will switch to a proof-of-stake model for security, reducing the issuance requirement to somewhere between zero and 0. Numbers can be at least 0 and at most 2 An attacker creates a very long infinite loop with the intent of forcing the miner to keep computing for such a long time that by the time computation finishes a few more blocks will have come out and it will not be possible for the miner to include the transaction to claim the fee. A transaction contains one or more inputs, with each input containing a reference to an existing UTXO and a cryptographic signature produced by the private key associated with the owner's address, and one or more outputs, with each output containing a new UTXO to be added to the state. This contract works as follows. The contract author does not need to worry about protecting against such attacks, because if execution stops halfway through the changes they get reverted. The Ethereum protocol would not "support" any of the applications directly, but the existence of a Turing-complete programming language means that arbitrary contracts can theoretically be created for any transaction type or application. The only argument against this type of network model from an economic standpoint is that wealthy individuals could control large portions of the network. Messages Contracts have the ability to send "messages" to other contracts. The client then undertakes the exact same procedure, but using the provided proof as its database ; if its result is the same as what the server claims, then the client accepts the proof.
The differences in monetary policy are some of the most profound and often overlooked variances between Bitcoin and Ethereum. The biggest of these operations is run by the makers of most of the worlds mining hardware, Bitmain. In Ethereum, highly gas-consuming blocks can also take longer to propagate both because they are physically larger and because they take longer to process the transaction state transitions to validate. In response to this, the co-owner of bitcoin. Bitcoin and Ethereum are the two most well-known cryptocurrencies today, with the former the legacy cryptocurrency created by the anonymous Satoshi Nakamoto in and the latter proposed by Vitalik Buterin in Merkle trees: Set it up as an Ethereum contract. What is the best zcash wallet that works with coinbase web wallet ethereum At launch After 1 year After 5 years Currency units 1. Subtract the neo community coin is dogecoin good to invest from the sender's account balance and increment the sender's nonce. The answer is that it allows for a neat mechanism known as Merkle proofs: The reason is that the state is stored in the tree structure, and after every block only a small part of the tree needs to be changed. Thus, if the block interval is short enough for the stale rate to be high, A will be substantially more efficient simply by virtue of its size. D[wiki] https: To show the motivation behind our solution, consider the following examples:
Happy Birthday:. Transfer the transaction value from the sender's account to the receiving account. The motivation behind GHOST is that blockchains with fast confirmation times currently suffer from reduced security due to a high stale rate - because blocks take a certain time to propagate through the network, if miner A mines a block and then miner B happens to mine another block before miner A's block propagates to B, miner B's block will end up wasted and will not contribute to network security. Their tech is also highly adaptable and being implemented in a number of other projects. Miners could try to detect such logic bombs ahead of time by maintaining a value alongside each contract specifying the maximum number of computational steps that it can take, and calculating this for contracts calling other contracts recursively, but that would require miners to forbid contracts that create other contracts since the creation and execution of all 26 contracts above could easily be rolled into a single contract. Merkle Trees! Produce another transaction sending the same BTC to himself 4. The application is simple: In response to this, the co-owner of bitcoin. Ether will be released in a currency sale at the price of ether per BTC, a mechanism intended to fund the Ethereum organization and pay for development that has been used with success by other platforms such as Mastercoin and NXT. An attacker takes over one of the data feeds, which is designed to be modifiable via the variable-address-call mechanism described in the section on DAOs, and converts it to run an infinite loop, thereby attempting to force any attempts to claim funds from the financial contract to run out of gas. However, the scripting language as implemented in Bitcoin has several important limitations:
Block difficulty growth chart illustrates just why bitcoin
This is because, as for any electronics, building ASICS involves mineral extraction, transportation, petrol-based and other toxic chemicals and so forth. Further Applications 1. The Hardware There are two ways in which one bitcoin 10 year growth can arrange their mining part time work from home belfast system. The anonymous e-cash protocols of the s and the s, mostly reliant on a cryptographic primitive known as Chaumian blinding, provided a currency with a high degree of privacy, but the protocols largely failed to gain traction because of their reliance on a centralized intermediary. Bitcoin's decentralized consensus process requires nodes in the network to continuously attempt to produce packages of transactions called "blocks". So instead, the attacker creates a "fork" of the blockchain, starting by mining another version of block pointing to the same block as a parent but with the new transaction in place of the old one. In , a decentralized currency was for the first time implemented in practice by Satoshi Nakamoto, combining established primitives for managing ownership through public key cryptography with a consensus algorithm for keeping track of who owns coins, known as "proof of work". Scripting Even without any extensions, the Bitcoin protocol actually does facilitate a weak version of a concept of "smart contracts". Bitcoin Growth Fund. Like a transaction, a message leads to the recipient account running its code. The BTC received from the sale will be used entirely to pay salaries and bounties to developers and invested into various for-profit and non-profit projects in the Ethereum and cryptocurrency ecosystem. The economic incentives exist for ASIC manufacturers to use such a trick to attack each other. This has two important benefits. We also theorize that because coins are always lost over time due to carelessness, death, etc, and coin loss can be modeled as a percentage of the total supply per year, that the total currency supply in circulation will in fact eventually stabilize at a value equal to the annual issuance divided by the loss rate eg.
In the near future, we expect "ether" to be used for ordinary transactions, "finney" for microtransactions bitcoin miner reward estimation calculator mining ethereum with a decrete motherboard "szabo" and "wei" for technical discussions around fees and protocol implementation; the remaining denominations may become useful later and should not be included in clients at this point. A more sophisticated name registration fractal bitcoin debt settlement bitcoin will also have a "function clause" allowing other contracts to query it, bitcoin binary challenge ethereum mining hash total well as government regulation cryptocurrency nvidia cryptocurrency algorithms mechanism for the "owner" ie. Although it is definitely theoretically possible to make a blockchain without Merkle trees, simply by creating giant block headers that directly contain every transaction, doing so poses large scalability challenges that arguably puts the ability to trustlessly use blockchains out of the reach of all but the most powerful computers in the long bitcoin mining for beginners 2019 litecoin pool alternate ports. Ethereum is likely to suffer a similar growth pattern, worsened by the fact that there will be many applications on top of the Ethereum blockchain instead of just a currency as is the case with Bitcoin, but ameliorated by the fact that Ethereum full nodes need to store just the state instead of the entire blockchain history. Yet the thread of a 51 percent attack is a concern shared across proof-of-work crypto networks and as mentioned above, some blockchains have been left exposed due to falling hash rates. Wait for party B to input bitcoin binary challenge ethereum mining hash total. The precise condition is that the double-SHA hash of every block, treated as a trukey bitcoin can i buy bitcoin on scottrade number, must be less than a dynamically adjusted target, which as of the time of this writing is approximately 2 The two main choices in the above model are 1 the existence and size of an endowment pool, and 2 the existence of a permanently growing linear supply, as opposed to a capped supply as in Bitcoin. Only when convenient? First, the mining ecosystem has come to be dominated by ASICs application-specific integrated circuitscomputer chips designed for, and therefore thousands of times more efficient at, the specific task of Bitcoin mining. Bitcoin and Ethereum retain the two largest open-source communities in the cryptocurrency sector. Although there are many ways to optimize Ethereum virtual machine execution via just-in-time compilation, a basic implementation of Ethereum can be done in a few hundred lines of free bitcoin cloud mining platform genesis mining com payouts. Thus, in general, between two adjacent blocks the vast majority of the tree should be the same, and therefore the data can be stored once and referenced twice using pointers ie. Happy Birthday: You may need to have a few thousand interlocking contracts, and be sure to feed them generously, to do that, but nothing is stopping you with Ethereum at your fingertips. This model is untested, and there may be difficulties along the way in avoiding certain clever optimizations when using contract execution as a mining algorithm. This would require an oracle to determine the value of 1 BTC ethereum explanation video can i use any graphics card to mine bitcoin USD, but even then it is a massive improvement in terms of trust and infrastructure requirement over the fully centralized solutions that are available. Over the course of development, our goal is to create a program where if one was to make a small protocol modification in one place, the application stack would continue to function without any further modification.
The motivation behind GHOST is that blockchains with fast confirmation times currently suffer from reduced security due to a high stale rate - because blocks take a certain time to propagate through the network, if miner A mines a block and then miner B happens to mine another block before miner A's block propagates to B, miner B's block will end up wasted and will not contribute to network security. The former approach, while reasonably successful in the what was the first purchase using bitcoin will be a bubble of applications like Namecoin, is difficult to implement; each individual implementation needs to bootstrap an independent blockchain, as well as building and testing all of the necessary state transition and networking code. This mechanism allows any non-cryptographic asset to be "uplifted" into a cryptographic asset, provided that the issuer can be trusted. A "full node" in the Bitcoin network, one that stores and processes the entirety of every block, takes up about 15 GB of disk space in the Bitcoin network as of Apriland is growing by over a gigabyte per month. Specifically, local bitcoin for other cryptocurrency ethereum to hit 1000 Antminer D3. Alice and Bob together can withdraw. Scripts can also be used to pay bounties for solutions to computational problems, and one can even construct a script that says something like "this Bitcoin UTXO is yours if you can provide an SPV proof that you sent a Dogecoin transaction of this denomination to me", essentially allowing decentralized cross-cryptocurrency exchange. Both Bitcoin and Ethereum use open-source improvement proposals from the community. Note that in the future, it is likely that Ethereum will switch to a proof-of-stake model for security, reducing the issuance requirement bitcoin binary challenge ethereum mining hash total somewhere between zero and 0. Reward to coinbase vitalik buterin ethereum allows for the creation of a cloud computing market where any user can participate with their desktop, laptop or specialized server, and spot-checking together with security deposits can be used to ensure that the system is trustworthy ie. Robert is News Editor at Blockonomi. Show comments Hide comments. The root of the tree depends only on the data, not on the order in which updates are. In response to this, the co-owner of bitcoin.
This is because most mining hardware today is made in China. This is essentially a literal implementation of the "banking system" state transition function described further above in this document. EVM code allows looping in two ways. This has a simple answer: Both Bitcoin and Ethereum use open-source improvement proposals from the community. What are the Differences? The proof-of-stake model means that anyone with consumer level hardware and a few units of PIV can participate on the network. Ethereum RLP: NASDAQ designed so that that party has the ability to update the contract as needed, and providing an interface that allows other contracts to send a message to that contract and get back a response that provides the price. A commonly asked question is "where" contract code is executed, in terms of physical hardware. Merkle trees are a fundamental part of what makes blockchains tick. Here is a blog post from Vitalik Buterin, the founder of Ethereum, on [Ethereum] https: Alice and Bob together can withdraw anything. Out of curiosity, was there any financial benefit to the writer s from PIVX foundation or any of their associates? The basic block validation algorithm in Ethereum is as follows:.
Additionally, we predict that ledger blue online web where is my jaxx wallet extension on chrome set of applications for decentralized consensus technology will follow a power law distribution where the vast majority of applications would be too small to warrant their own blockchain, and we note that there exist large classes of decentralized applications, particularly decentralized autonomous organizations, that need to interact with each. The contract would read these values from the message data and appropriately place them in storage. While the topic of mining centralization may be controversial to some, it is a simple truth that the more centralized something becomes, the easier it is to shut. This makes it hard to make multi-stage options contracts, decentralized exchange offers or two-stage cryptographic commitment protocols necessary for secure computational bounties. This is because network domination would require a massive majority ownership of almost all available PIV units. It also means that UTXO can only be used to build simple, one-off contracts and not more complex "stateful" contracts such as decentralized organizations, and poloniex discussion when did coinbase begin business meta-protocols difficult to implement. Any optimization which adds complexity should not be included unless that optimization provides very substantial benefit. The issuance model will be as follows: This article won't go into the detailed specification; that is best done by this article and this onethough I will discuss the basic reasoning. Learn how to calculate your crypto mining profitability Report: An important feature of the protocol is that, although it may seem like one is trusting many random nodes not to decide to forget the file, one can reduce that risk down to near-zero by splitting the file into many pieces via secret sharing, and watching the contracts to see each piece is still in some node's possession. It does this by substituting a formal barrier to participation, such as the requirement to be registered as a unique entity on a particular list, with an economic barrier - the weight of a single node in the consensus voting process is directly proportional to the computing power that the node brings. Other, more complicated, scripts exist for various additional use cases. Ethereum does this by building what is essentially the ultimate abstract foundational layer: This allows for the creation of a cloud computing market where any user can participate with their desktop, laptop or specialized server, and spot-checking together with security coinbase omisego how to buy cryptocurrency other than bitcoin can be used to ensure that the system is trustworthy ie. But it could still incur that large energy cost that is associated with proof-of-work mining. One particular limitation is that, while they can bitcoin binary challenge ethereum mining hash total the inclusion of transactions, they cannot prove anything about the current state eg. Over the course of development, our goal is to create a program where if one was to make a small protocol modification in one place, the application stack would continue to function without any further modification. It would maintain a record of all open storage changes, along with a list of who voted for. At this point, the merchant will accept the payment as finalized and deliver the product; since we are assuming this is a digital good, is mining gold profitable is mining with gpu profitable is instant.
Thank You again. Notify me of follow-up comments by email. Bitcoin and Ethereum are the two most established cryptocurrencies today. This contract works as follows. Out of curiosity, was there any financial benefit to the writer s from PIVX foundation or any of their associates? Especially the kinds that rely on a single point of failure. Org February 15, at Oliver Dale January 29, at 3: Here, instead of a single issuer providing the funds to back up an asset, a decentralized market of speculators, betting that the price of a cryptographic reference asset eg. Mining is quickly becoming more of a problem than a solution. The security of our network essentially depends on them acting honourably, and us being prepared to respond to it. Ethereum Merkle Patricia trees: For those cryptocurrencies that are lucky or unlucky enough to have ASIC miners, the centralization of proof-of-work mining seems to be an inevitability. Want to set up a full-scale Daemon or Skynet? Bitcoin Mining — Is it worth it? The basic block validation algorithm in Ethereum is as follows:. Alternative Blockchain Applications The idea of taking the underlying blockchain idea and applying it to other concepts also has a long history.
Note that in reality the contract code is written in the low-level EVM code; this example is written in Serpent, one of our high-level languages, for clarity, and can be compiled down to EVM code. Since Bitcoin's underlying cryptography is known to be secure, the attacker will target the one part of the Bitcoin system that is not protected by cryptography directly: The countdown is finally complete and Bitcoin Growth Bot is live! However, there was unfortunately no effective replicated database system available at the time, and so the protocol was never implemented in practice. The fundamental unit of computation is "gas"; usually, a computational step costs 1 gas, but some operations cost higher amounts of gas because they are more computationally expensive, or increase the amount of data that must be stored as part of the state. Earlier buyers will benefit from larger discounts. Ethereum is useful for making dapps that have various use cases. Contract accounts are smart contracts that are run by code and programmed to receive, store, and contact other accounts in the network based on certain inputs. Additional proposals for layer two scaling of Ethereum include Plasma and dappchains which would supplement the on-chain throughput of the network by localizing consensus to specific dapps and childchains tethered to the root chain. The downside? Additionally, Turing-incompleteness is not even that big a limitation; out of all the contract examples we have conceived internally, so far only one required a loop, and even that loop could be removed by making 26 repetitions of a one-line piece of code.
